LanScope Cat IT資產管理和資料丟失預防軟體
由日本 MOTEX Inc. 公司開發的 LanScope Cat 軟體功能強大,主要功能有 Asset Management 資產管理、Operations Log Management 日誌管理、Web Access Management 訪問管理,及 Device Control。
軟體可以綜合管理IT資產,自動收集 IT 設備內部重要信息,操作日誌管理 Web 訪問管理、設備控制、電子郵件管理、應用程式 ID 監察等主要功能,以及伺服器 Log 訪問日誌管理、文件伺服器容量管理、域名登錄,註銷管理等多個特色功能,針對已知和未知的惡意軟體防護,為企業內部資料洩漏施以對策方案,有效解決資訊安全問題。
軟體工具檢測惡意軟體,追蹤進入通路的隔離。有些不能完全防止惡意軟體的新物種繼續在傳統的反病毒措施成長,某些情況下,不知道感染。這是一個挑戰,即使知道有病毒感染,可能需要很長的時間來確定原因。LanScope Cat 軟體擁有IT網路管理和資料丟失預防工具的強大功能,提供企業防毒及資料洩漏和丟失預防的最佳解決方案。
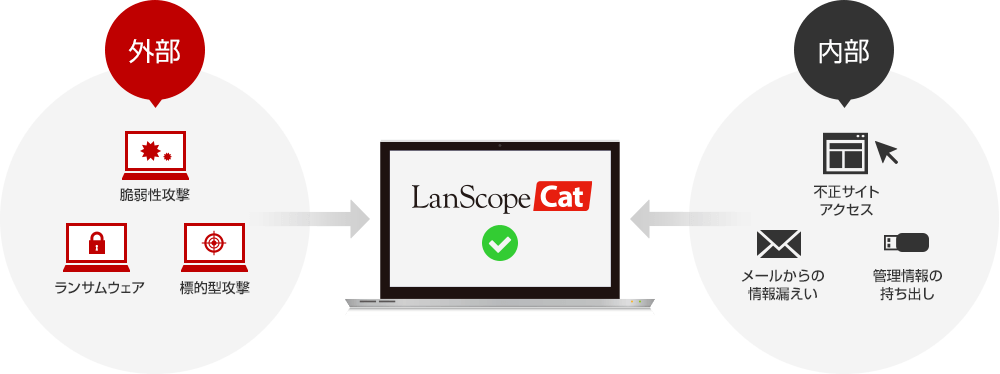
The actual causes of information leaks are mostly employees or contractors who bring out data in e-mail or recording media or copies of paper materials. As described above, companies suffer great damage due to information leaks. These costs are not only in the form of apologizing to victims and investigation costs, but in the loss of trust in the company and brand image. The effect on a company of just one information leak is immeasurable. And 80% of them are caused from the inside.
- Manage IT assets
- Monitor asset performance
We automatically collect information to ascertain usage status of IT assets, including PCs and software, and create an environment to render the best performance by setting up the right resources in the right places.
- Employee monitoring
- Productivity management
By recording computer usage, we can suppress illicit and non-business use. Also, we learn about and analyze usage of IT assets and work status, creating improved operational efficiency and productivity.
- USB control, app control
- Control of data removal
By visualizing data usage and controlling routes through which information can leak (Web, devices, apps, PCs), we protect personal information and your company's secret information.
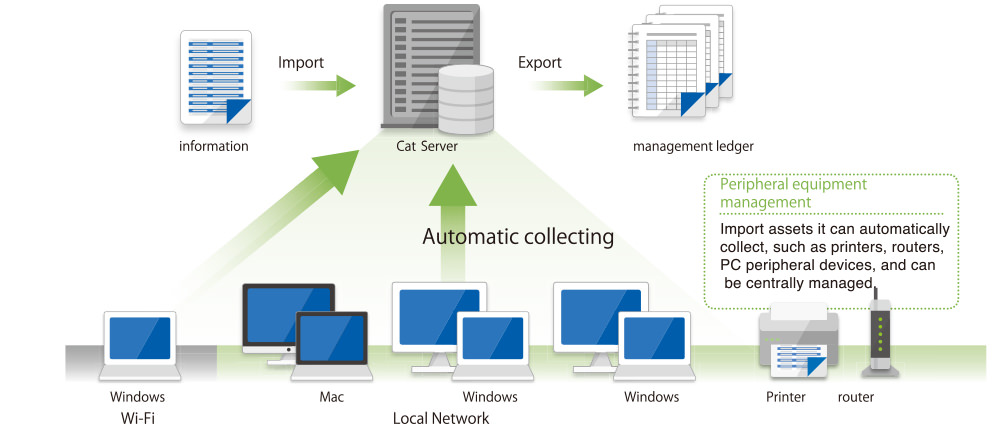
資產管理
每天更新硬體和軟體信息,以維護準確的環境,而無需管理任務的麻煩。自動收集IT資產信息並始終查看準確的信息。此外,保留更改歷史記錄並通過電子郵件通知管理員。可以導入現有日誌或導出每一代中的日誌。
硬件資產信息
自動收集50多種類型的硬式信息,例如電腦名稱和IP地址,以及可選的設置註冊表數據。可選擇記錄和管理影印機和其他外圍設備。此外,可以通過搜索各種條件來檢查必要的信息。
軟體管理
檢查程式更新,消息和問卷,以及是否在PC上安裝了程式更新。對允許和禁止的應用進行分類並管理信息,例如每個應用安裝的機器數量及其產品密鑰。
消息和調查
向管理員發送問卷給用戶。
- 使用免費回復和下拉菜單進行問卷調查,以收集無法自動收集的信息,例如身份證號碼和負責資產的部門。
- 確認後,響應將反映在資產分類帳中。
外圍設備管理
在一個地方管理影印機,路由器和PC外圍設備。導入無法自動收集的資產數據。
硬體資產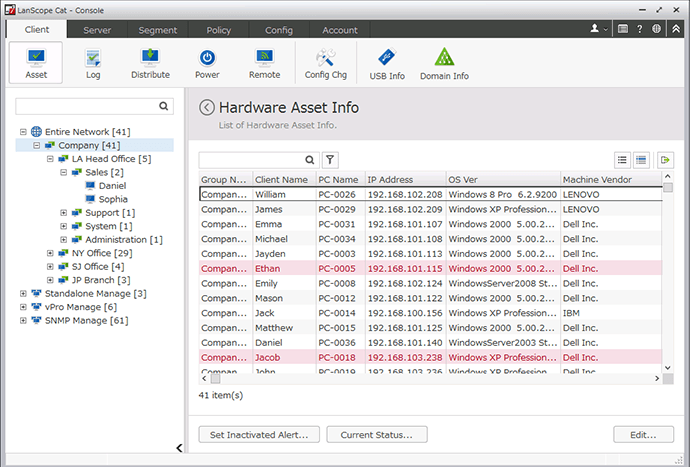
信息自動收集50多種類型的硬體信息,例如電腦名稱和IP地址,以及可選的設置註冊表數據。可選擇記錄和管理影印機和其他外圍設備。此外,可以通過搜索各種條件來檢查必要的信息。
軟體管理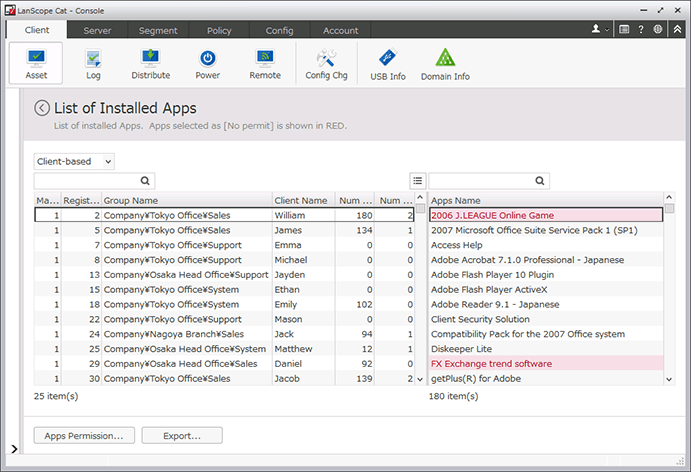
檢查程式更新,消息和問卷,以及是否在PC上安裝了程式更新。對允許和禁止的應用進行分類並管理信息,例如每個應用安裝的機器數量及其產品密鑰。
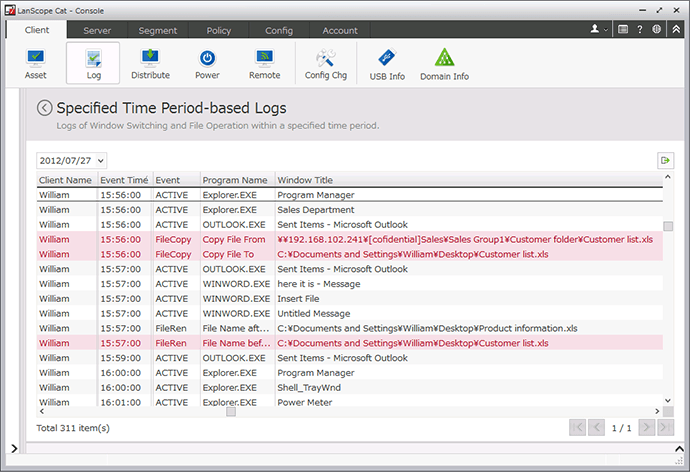
操作日誌管理
通過管理PC操作日誌,可以在不降低運營效率的情況下提高安全性並在緊急情況下發現問題。
記錄PC使用信息,例如運行的應用程式,影印,文件操作,屏幕視圖(窗口標題)。如果存在任何操作違規,則會向用戶顯示警告,從而提高安全性和道德性。此外,還會實時通知管理員,從而可以防止潛在的嚴重問題。
操作日誌管理
記錄“誰”在“哪台PC”處“做什麼”“何時”。如果發生可能是信息洩漏的某些操作違規,例如將客戶列表寫入USB,則向用戶顯示警告,並且防止非法操作。
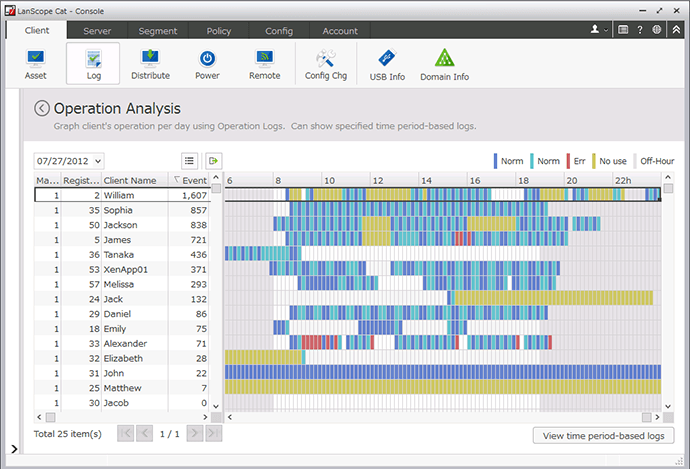
運營分析
在彩色編碼圖中查看PC的狀態。
影印日誌管理
記錄“誰”在“哪台PC”上影印“什麼”“何時”打印“多少頁”。發現浪費的影印並降低成本。如果影印特定文件,則向用戶顯示警告並防止非法影印。
應用使用管理
在“哪台PC”上記錄“誰”使用“哪個應用程式”“何時”。查看每台應用在PC上運行的實例數量以及持續時間。通過分配理想數量的許可證來減少浪費的許可證成本。
App禁止
禁止發布與工作無關的非法應用或應用。如果啟動了特定應用程式,則會向用戶顯示警告,並且會抑制諸如游戲之類的應用程序或可能導致信息洩漏的應用程式。
Web訪問管理
監控網站使用情況,並限制對非法網站的訪問。
可以記錄訪問的網站並控制對特定網站或網站類別的訪問。促進用戶使用適當的網站,避免訪問有害網站。
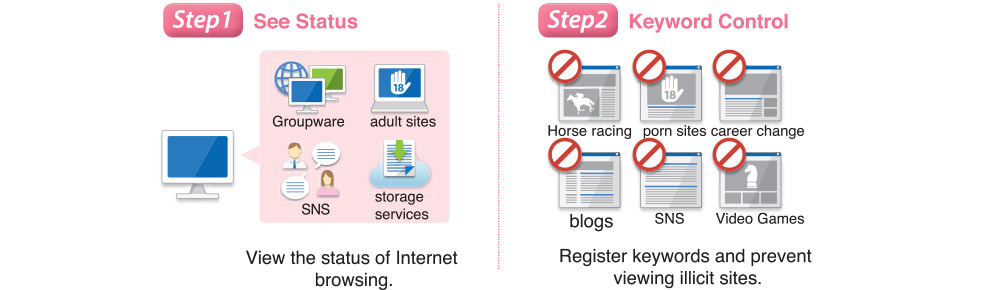
Web訪問管理/控制
記錄“誰”在“哪台電腦上”查看“哪個網站”“何時”。如果查看非法網站,則可以顯示警報或阻止訪問。此外,可以限制上載和下載,並記錄在Internet Explorer中發佈到Web的信息。
白名單
指定關鍵字僅允許訪問特定網站。
創建一個只能訪問工作所需的網站(例如群件和雲端服務)的環境。
檢查已查看的Web內容
通過單擊Web訪問日誌中的URL並直接查看Web站點,可以判斷Web內容是否是工作所必需的。
分析查看的Web內容
通過查看按日,小時或PC排序的報告,查看網站查看數據的趨勢。此外,在每個報告中,查看有多少百分比的網站包含警報關鍵字。
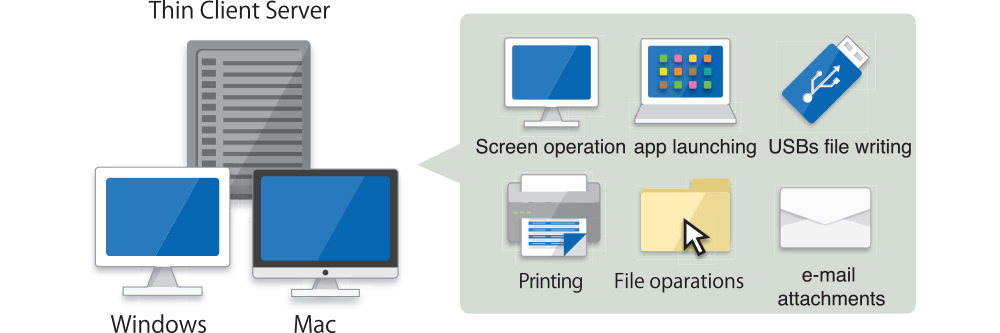
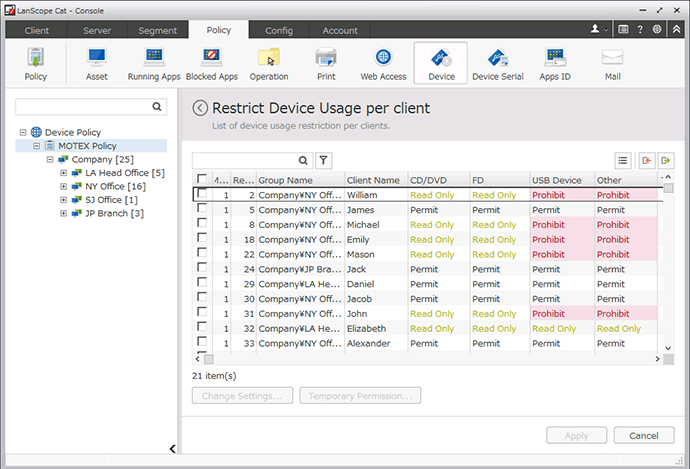
設備控制
控制USB和CD等設備的使用,防止重要的秘密信息洩露。
管理所有公司設備並限制其使用。如果連接了禁止的設備,則通知用戶禁止該設備並控制非法使用。此外,通過PC和設備設置詳細條件以適應工作場所,允許在有限的情況下使用設備。
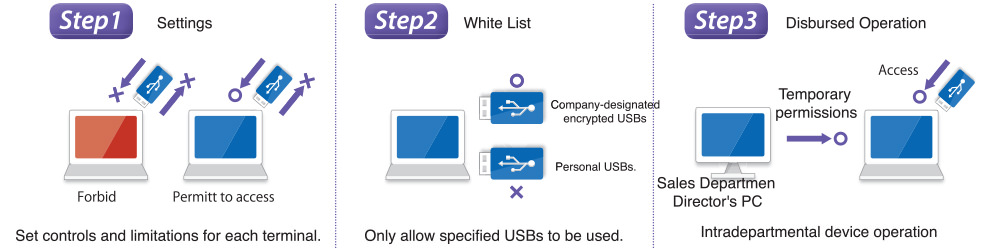
設置每個終端的使用限制
按類型控製或禁止使用CD,DVD,USB等。此外,靈活的設置允許每台PC設置為禁用讀取和寫入,僅禁用寫入等。
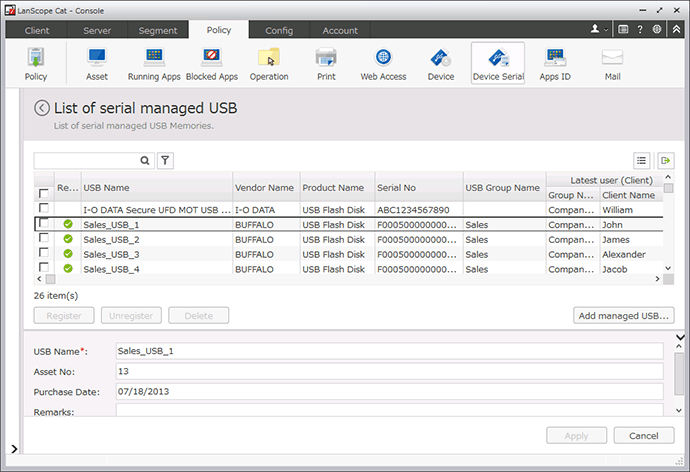
設置USB權限
指定設備名稱(暱稱),製造商編號(序列號),或僅允許公司發布的設備,並禁止使用和連接其他設備。
USB連接信息
顯示連接到託管PC的USB列表,查看哪些USB是允許的USB,哪些是不允許的。
還輸入和編輯管理所需的信息,例如用戶或資產編號。
USB管理器的工具
管理人員可以允許,拒絕或臨時允許他們通過PC管理的USB。
| System Environments ※for 100 clients | ||
| Manager Sub-manager Web console |
OS | Windows Server 2012 Windows Server 2012 R2 Windows Server 2008 Windows Server 2016 Windows Server 2019 |
| CPU | 2.0GHz or higher | |
| Memory | 4GB or more | |
| Storage | 200GB or more | |
| Database | SQL Server 2012 SQL Server 2014 SQL Server 2017 SQL Server 2019 |
|
| Web console (browser) |
Google Chrome Mozilla Firefox Microsoft Edge |
|
| Agent | OS |
【Windows】
|


