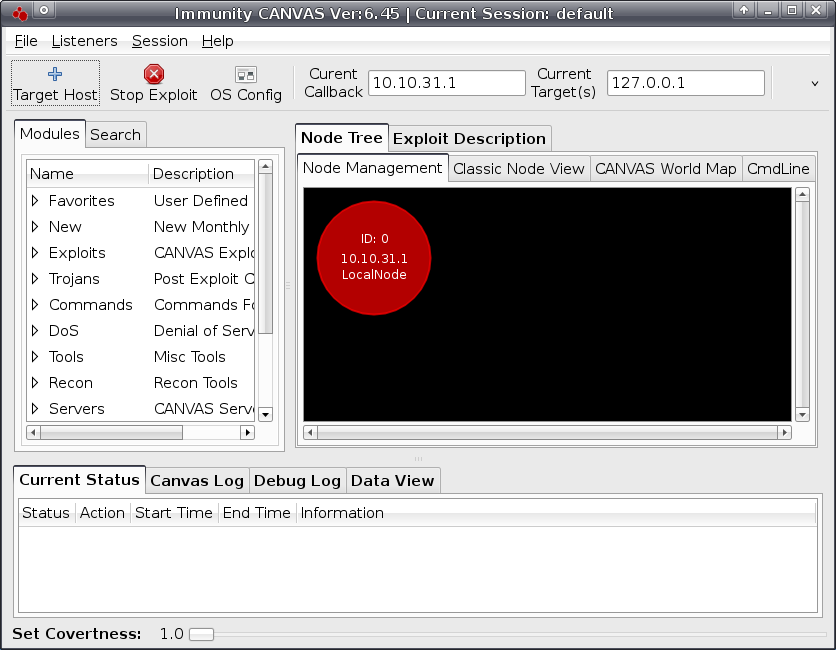
Immunity Canvas 是 一套安全漏洞滲透測試工具。Canvas滲透測試工具包含480個以上的漏洞利用, 並包含作業系統、應用軟體等大量的安全性漏洞。對於滲透測試人員來說,Canvas是比較專業的安全性漏洞利用工具。其也常被用於對IDS和IPS的檢測能力的測試。每個月會將穩定的版本及時發佈,通過Web網站進行更新,同時更新漏洞利用模組和引擎程式。並且會及時發郵件提醒用戶使用。
主要功能
- 自動攻擊:可以選擇自動攻擊功能,軟體會自動對網路、作業系統、應用軟體進行攻擊。
攻擊成功後,會自動返回目標系統的控制權。 - 漏洞攻擊:該軟體漏洞庫每天進行更新。同時包含了大量的0day以及未公開的漏洞。可以指定漏洞對目標系統進行攻擊。
- 升級功能:該套裝軟體含兩種升級方式,月度升級和即時升級。“月度升級”指每月升級一次,適合研究機構和小型企業使用。
“即時升級”基本上每天更新一次,包含0DAY漏洞和未公開漏洞,適合滲透測試團隊和攻防團隊使用。
Exploits
- currently over 490 exploits, an average of 4 exploits added every monthly release
- Immunity carefully selects vulnerabilities for inclusion as CANVAS exploits. Top priorities are high-value vulnerabilities such as remote, pre-authentication, and new vulnerabilities in mainstream software.
- Exploits span all common platforms and applications
Payload Options
- to provide maximum reliability, exploits always attempt to reuse socket
- if socket reuse is not suitable, connect-back is used
- subsequent MOSDEF session allows arbitrary code execution, and provides a listener shell for common actions (file management, screenshots, etc)
- bouncing and split-bouncing automatically available via MOSDEF
- adjustable covertness level
Exploit Delivery
- regular monthly updates made available via web
- exploit modules and CANVAS engine are updated simultaneously
- customers reminded of monthly updates via email
Exploit Creation Time
- exploits included in next release as soon as they are stable
Effectiveness of Exploits
- all exploits fully QA'd prior to release
- exploits demonstrated via flash movies
- exploit development team available via direct email for support
Ability to make Custom Exploits
- unique MOSDEF development environment allows rapid exploit development
Hardware
CANVAS runs well on any modern hardware. The simple question is to ask yourself how well your hardware runs your chosen operating system. If your hardware runs your OS well, then CANVAS will run well. Here are some minimum specs.
- 1.2ghz processor
- Chip architecture/OS must have Python 2.5 or greater support
- 1GB RAM
- 250mb free HD space
- Good Linux drivers for wired/wireless cards
Supported Platforms and Installations
- Windows (requires Python & PyGTK)
- Linux
- All other Python environments such as mobile phones and commercial Unixes (command line version only supported, GUI may also be available)
Immunity Debugger
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility.
CANVAS 3rd Party Products
DSquare Security
D2 Exploitation Pack
D2 Exploitation Pack helps enterprise to replicate real life attacks during penetration tests by providing powerful and efficient exploitation tools, validating vulnerability scans and revealing which data would be at risk.
D2 Elliot
D2 Elliot Web Exploitation Framework helps enterprise to replicate reallife attacks during web application penetration testing by providing a powerful framework and efficient exploits and tools, validating vulnerability scans and revealing which data would be at risk.
Gleg
Agora
While providing security specialists with 0days, GLEG acknowledges that there is a certain interest to exploits for vulnerabilities discovered by third party researchers. To meet this interest GLEG has made available the "Agora Pack".
The Agora Pack contains more than 80 exploit modules from the product known as "Argeniss 0day Exploits Pack", along with exploits for fresh publicly available vulnerabilities and 0days exploits discovered by GLEG. Modules are designed to be used with Immunity CANVAS. Agora content does not intersect with VulnDisco Pack Professional.
Agora SCADA+ Pack
The SCADA+ pack speaks to this new trend by providing its customers with exploits for both public vulnerabilities and 0day vulnerabilities in SCADA systems. If you serve an industry that does any type of automation, the SCADA+ pack should be on your radar for running the most realistic attack scenarios and penetration tests for your customers.
- Growing value ~350 exploits currently
- Due to low real systems patch rank exploits are actual for a longer time
- We try to cover most of the public SCADA vulns!
- Including old and newly discovered bugs
- 0 Days for SCADA
- We conduct our own in depth research
- Focused on Industrial software & hardware environment
- Not only SCADA, but also Industrial PCs, smart chips and industrial protocols are reviewed.
- Weak points analyses
- Many industrial things suffer from weaknesses like hardcoded password and etc.
DefPack
In an attempt to provide pen testers with a most comprehensive collection of Defense software vulnerabilities illustrated GLEG created the DefPack Exploits Package. Anti-viruses, IDS and IPS systems, Firewalls, Account Management systems, End-point protection software and more are targeted. Defense Software is very special due to its wide usage and critical nature. The pack contains mostly exploits for public vulnerabilities along with some 0days discovered by GLEG.
- Critical value: Ability to test your defense software and to measure real threat
- Nicest public Defense software vulnerabilities coverage! Including old and newly discovered bugs
- 0 Days exploits: We conduct our own in depth research and provide you with tools and sploits, which could be helpful for Defense software pentesting.
- Weak points analyses: Some systems suffer from weaknesses like hardcoded passwords and etc. We provide tools to test such cases.
MedPack
The MedPack is an attempt to collect most medical software vulnerabilities in a one exploit Pack. GLEG covers the software that is widely used in Medical Care and Dental accounting. This Pack could be of interest for security specialists working in this particular field.
- Most of vulns are 0days discovered by GLEG.
- Growing value - Due to low real systems patch rank
- We try to cover most of the public Medical vulns! Including old and newly discovered bugs
- 0 Days exploits for Medical software vulnerabilities. We conduct our own in depth research!
- Weak points analyses. Some systems suffer from weaknesses like hardcoded passwords and etc.
InteVyDis
VulnDisco Pack
VulnDisco Pack Professional is the Immunity CANVAS add-on which consists of more than 300 modules targeting unpatched vulnerabilities.
- The richest set of exploits for unpatched vulnerabilities available on the market.
- Targeted on well known software products.
- Client side and server side vulnerabilities.
- Updated once a month.
ProtoVer Pack
The ProtoVer Test Suite combines the results of InteVyDis's complied work over the years.
- Network protocols tests: DNS, DHCP, IMAP, LDAP, NFS, RADIUS, SMTP, SNMP, SOCKS, SSH, SSL and more
- File formats tests: ACE, ALZ, ARJ, CAB, CHM, DOC, GZ, HLP, LHA, RAR, ZIP, ZOO, PPT, ELF, PE, TNEF, WMF and more
- written in pure Python and provided with full source code
VulnDisco Step Ahead
With the Step Ahead Pack, all modules are provided under the terms of Developer license, which allows you to create patches, workarounds, signatures and use them for commercial needs.
- 1 year of updates and support
- Up-to-the-minute information: You will receive all the information being developed for VulnDisco Pack Professional on the earliest stage of development. Some exploit modules from SA never appear in normal VulnDisco Pack Professional.
- VulnDisco Pack Professional unlimited Developer license with 1 year of updates and support
- ProtoVer testsuite unlimited license with 1 year of updates and support
Tenable Network Security
Tenable: Nessus
Nessus, the industry’s most widely deployed vulnerability scanner helps you reduce your organization’s attack surface and ensure compliance in physical, virtual, mobile and cloud environments. Nessus features highspeed asset discovery, configuration auditing, target profiling, malware detection, sensitive data discovery and vulnerability analysis. With the world’s largest continuously-updated library of vulnerability and configuration checks, and the support of Tenable’s expert vulnerability research team, Nessus sets the standard for speed and accuracy. Nessus supports more technologies than competitive solutions, scanning operating systems, network devices, hypervisors, databases, tablets, phones, web servers and critical infrastructure for vulnerabilities, threats and compliance violations.
Nessus supports more technologies than competitive solutions, scanning operating systems, network devices, hypervisors, databases, tablets, phones, web servers and critical infrastructure for vulnerabilities, threats and compliance violations.


